Data Governance
Data Governance focuses on getting the most out of information at the least cost while keeping it secure.
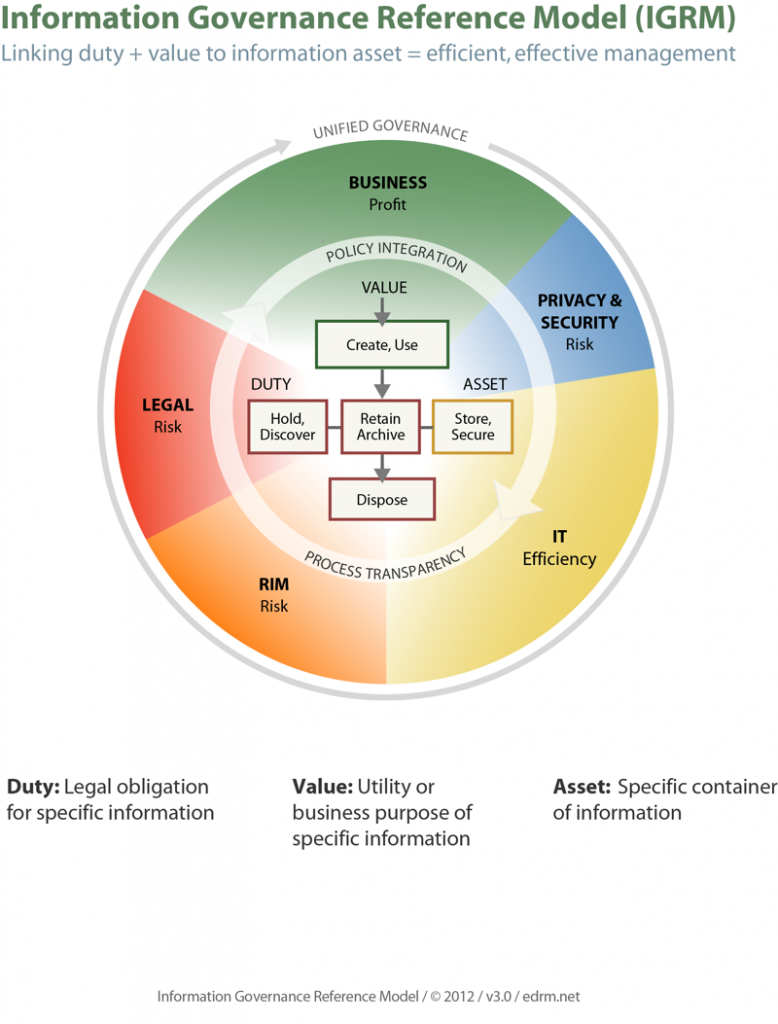
It’s about minimizing information risks and costs while maximizing its value. Data governance is control of information to meet legal, regulatory, risk, and business demands. It means that business risk and security considerations and an organization’s appetite for risk, such as the likelihood of data breaches are built into information handling procedures.
In summary it is ensuring security, control, and optimization of information (Robert Smallwood)
Good Information governance principles
First and foremost is executive sponsorship. That executive sponsor needs to have a long-term commitment and they must own the business case or the investment justification for the program. Sponsorship helps clear obstacles, as you move forward.
The second principle that’s required for information or data governance programs is stakeholder consultations.

That means that you’re going to go out into those business units and also into these functional areas such as legal, IT, privacy and security, and records and information management and determine what their information needs are and what information or data governance principles and activities you can implement to help them do their job better and contribute toward the completion of business objectives.
Another information governance principle is information policy development and its widespread communication. One needs to develop clear policies for access and use of information.

Those policies must be communicated regularly and crisply. When needed participants may need to be trained in them and the policy need to be reinforced on a consistent basis.
Information integrity. This means that information is accurate, correct, authentic, that it’s trustworthy and if you can provide that information to decision-makers they’ll have the confidence that information is based on trustworthy and accurate data.

One may want to maintain only unique data to reduce risks, reduce storage costs, and reduce your IT labor costs. In other words, you only need one single version of the data and all reports or other uses of that data would be based on that single instance.

Having a standard taxonomy also helps in ensuring integrity.
Overall, all information needs to be categorized, it needs to be as simple as walking into a library where you can go to the card catalog and find what you need within a few minutes. The organization should be just that organized in terms of information.
Another principle is metadata management which is crucial, so one needs to have a sound metadata strategy. Metadata describes a document or record, and as I mentioned earlier, it’s data about data. In other words, information that tells you about a document, things like the topic, the author, the date, the length, the file type, and so forth.
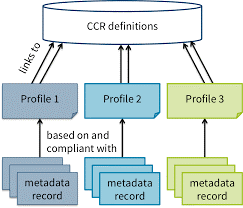
So metadata and standardizing your approach as to what’s needed within your organization is quite crucial. You have to standardize it, you have to keep it up to date because things change, business conditions change, you have mergers and acquisitions, those kinds of things.
Another principle is the record retention schedule, in the records and information management field. That RRS spells out how long particular file types or file series should be retained and what is done at the end of their useful life cycle.

There are three things that can be done at the end of the life cycle of a document or a record. It can be archived, meaning it’s preserved. It can be transferred, which happens in government agencies, or it can be disposed.
Information security and privacy, another key principle, one needs to secure information in its three states, at rest, in motion, and in use, so that even when you’re transmitting information, it’s protected, and particularly confidential information. If an employee loses a laptop or a mobile device that has confidential information on it, if proper IG policies are enforced using security related information technologies that information can be secured.
Information security is closely related to information privacy. So, it’s critical when you’re dealing with personally identifiable information and protected health information or credit card information and other confidential and sensitive information that you know where it is and that you lock it down with encryption and in the case of PII there are certain privacy laws that you not only need to protect but you also need to dispose of that information once you’re done with it in a certain time frame.
The principle of Information accessibility helps to lock down information, the control of information should not halt the flow of business, so you have to balance accessibility with information security. Accessibility is vital in the short-term but another issue that is often not considered is long-term digital preservation. So if there are documents or records that need to be kept for regulatory reasons, for safety reasons, and so forth, then you need to delve into long-term digital preservation for that information. Also, another element of information accessibility is controlling access to confidential documents and that’s done through IAM, identity access and management software.

Accessibility includes access controls, In other words, delivering the right information to the right people at the right time and keeping confidential or sensitive information out of hands of people who should not have access to it.
A principle for frequent Monitoring and Auditing can help in ensuring that there is no spoliation, ie. ensuring a document or record may not be altered without proper oversight and by only the right people for reasons that are valid. Changes need to be logged to ensure there is adequate provenance to prove the chain of custody.
The act of data Governance is a process of Continuous Improvement and always ongoing, they’re evergreen in a sense. It is not a one-time project although there may be some sub-projects to implement these principles.
Best Practices
Listed below are some proven best practices that have been shown to be effective in data Governance programs
First Best Practice is ensuring Executive Sponsorship. .
No program can succeed without a clear executive sponsor, and that sponsor must have long-term commitment. They must own the business case and the investment justification for the data Governance program.
An data Governance program is not a project, but rather an ongoing program.
As a best practice regular reviews should be conducted and adjustments should be made. data Governance program is an ongoing program, not a discreet project. Continuous improvement should be a goal.
Another best practice is to ensure frequent and productive interaction among the Cross Functional teams
Representatives from these functional groups, such as Legal, Records and Information Management, Information Technology, Privacy & Security, and your Business units must be involved. And, depending on your deployment and your implementation, there may be other groups involved, for instance, Human Resources for training and communications. If there is a Knowledge Management team it should be tasked with retaining lessons learned.
Establishing a practice of Defensible Deletion of data debris that no longer has value is critical in this era of big data. You must get rid of that garbage to be able to focus on high-value information and reduce your storage and labor costs.

Policies should be independent of information technology. Focus should be on improving the business processes with a clean sheet of paper without the constrictions or constraints of a particular technology.
Should always look for the best way to do it, and then look for technologies that can assist, and those technologies should help you to enable data Governance elements, such as monitoring, auditing, and enforcing your program.
RRS and LH: Records Retention Schedule and Legal Hold Notification program are two primary elements in an data Governance program. A Records Retention Schedule lists out the types of documents and records by file series. And how long they need to be kept. Legal Hold Notification is another key element, and that includes notifying employees when a lawsuit is initiated and freezing the information that may be called upon in that lawsuit.
Risk Planning Information Risk Mitigation Plan is a critical part of data Governance planning. Information Risk Mitigation Plan, helps to identify the risks to your information, for instance, breaches. Determine how likely and what the cost may be. And then consider countermeasures to be able to offset that risk.
Proper metrics, to be able to measure how you’re doing. are required, they’ll tell you how well you’re doing in terms of conformance or compliance to your program. You must use relevant metrics, and they need to be monitored on a regular basis.
Privacy by Design, this is really the idea that you bake in Privacy considerations into your business processes. And this is critical when you are trying to protect confidential and personal information like protected health information, personally identifiable information, credit card information, and that should be baked into your, or inserted into your business processes.
Should aim to standardize your metadata. That’s a best practice. Creating standardized metadata terms should be a part of your IG effort that enables faster, more complete, and more accurate searches, and retrieval of records.
As a best practice IG programs must be audited. Perhaps you have a third party, or you have an internal audit team, but they can provide you hard data on the results and feedback to help you improve. Should aim to make it a positive thing so you continue to fine-tune and improve your program, but at some times, you may need to implement punitive measures to people who simply won’t change or are non-compliant.
There is always a need to be able to protect information at all times in its three states, at rest, in use, and in transit. Encryption is a best practice to help improve the odds for success. They’re based on research and experience with organizations that have gone down the data Governance road. And, the set of Data Governance Best Practices will continue to grow and evolve.
Optimizing Information Value
Benefits of Data Governance (Information Governance)
Information Governance programs help to optimize information value as well. You reduce the irrelevant data debris, or dark data, which is unclassified or unorganized information and improve the information quality by focusing on that information that has high value. You can leverage information because you use business analytics and other tools to be able to find new insights. And you improve the cross-functional collaboration between legal, RIM, IT, privacy and security, and other business units.
Information programs improve legal functions, which are focused on minimizing legal risks and costs. Improving legal posture, helps to better prepared and better organized. Your information collection is organized and improves your ability to protect personally identifiable information, which you have privacy laws that you must be able to adhere to. Attorneys will spend more time on strategy and less time on rote tasks, such as combing through information.
Applying the principles and best practices will lead to improved security in information technology. There needs to be periodic vulnerability testing to find holes where patches may need to be able to be applied. Will help leverage business intelligence tools and improve decision-support for insights better that also improves efficiency in your overall information technology operation. Will lead to benefits, in the Records and Information Management Department. Improved data quality,
Justifying your investment in data governance programs by focusing on what is called ROT in the data governance community, which is redundant, obsolete, or trivial information. An easy win usually is by use of file analysis softwares. File analysis software will go out and scan all the files in your organization across your network attached drives, your shared drives, your storage area network, or any other storage devices.

This leads to reduction in expenses primarily in the management and storage of information.
1 Reduced storage costs because you’re reducing your information footprint.
- Reduced E-discovery costs during litigationbecause you have less information to be able to go through.
- Reduced compliance costsbecause it’s easier to find informationand produce it for regulators.
- Reduced security costs because youhave a more streamlined operation.You understand and know where your information is stored and it’s classified and organized properly.
- The privacy costs are going to be reduced as wellfor compliance and privacy laws.
- Will also lead to a reduced information risk.
In a Bank for instance, Business Units could be Retail Banking, Commercial Banking, Mortgage Lending, Trusts, Investments, and so forth. IG efforts here must include a focus on data quality, that is, getting good, clean data, that will later be used in downstream reports and analyses. These Business Units may be able to find new ways to innovate and create new products and services, based on insights they might find, by sifting, sorting, and distilling clean data.
In gist by ensuring security, control, and optimization of information there are many direct and tangible benefits that can provide great ROI on this ongoing activity.